How account takeover fraud works
There are many types of fraud, but account takeover fraud is one of the most common. This occurs when cybercriminals illegally access your accounts without your permission.
“The fraud happens when they use that access to take actions as the user that the user did not authorize, such as stealing money, data, or accessing other systems or accounts,” said Brad Lassiter, CEO of LastTech.
Once they have access to your accounts, they can steal your personal data for malicious use.
ATO fraud can impact several types of financial accounts.
- Bank accounts
- Payroll accounts
- Investments accounts
- Retirement accounts
- Health savings accounts (HSAs)
- Social media accounts
- Email accounts
- Unemployment benefits
A 2025 study by Security.org reveals that about half of all ATO cases reported involved social media accounts, with bank accounts coming in second.
The study also names identity theft as the top consequence of account takeover fraud, with financial losses and subsequent account takeovers following.
How criminals access your accounts
Cybercriminals can access your accounts in several ways:
- Data breach. Unfortunately, data breaches happen frequently today, which means your information could be stolen at any time by cybercriminals to sell on the dark web.
- Brute force attacks. Cybercriminals can gain access when you have weak passwords and no multi-factor authentication. They can employ bots to try multiple passwords until they land on the right one.
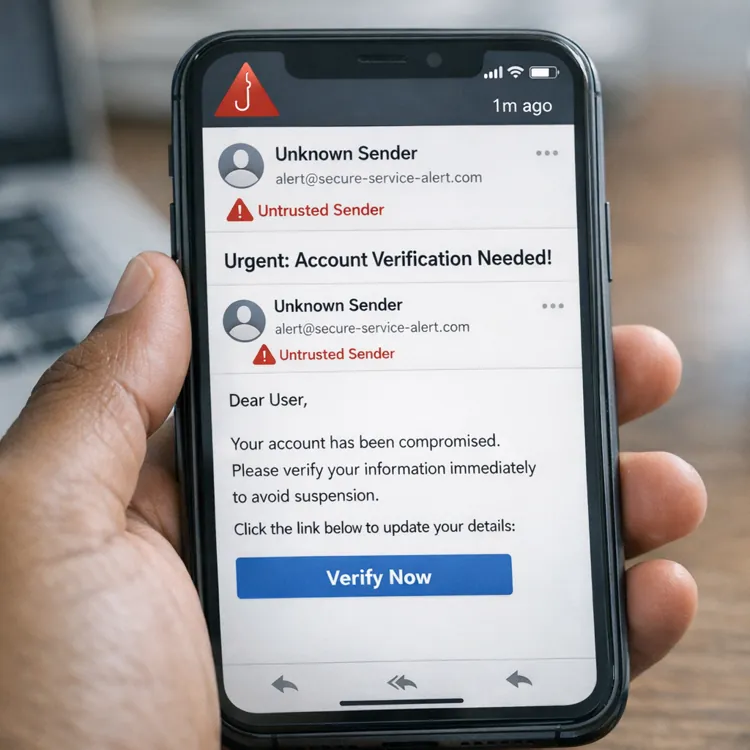
- Phishing. Phishing occurs when a cybercriminal sends a fake email designed to fool you into revealing your login and password. They may also set up a phishing website designed to look like an online banking or payroll site, so you provide your login information.
- Malware. Users may download software that appears legitimate but is actually malware that steals their information. With this, cybercriminals can steal funds and paychecks, resulting in significant financial losses.
- Social engineering. This involves a cybercriminal posing as a bank employee or customer support representative to solicit your login details.
- Search Engine Optimization (SEO) Poisoning ATO. Cybercriminals use advertisements to appear as a legitimate company. Pay attention to the web address carefully before clicking on a site, as SEO Poisoning uses fraudulent website URLs that look or are spelled very similarly to the legitimate site.
Kevin Gosschalk, founder and CEO of Arkose Labs, a cybersecurity company, explained how SEO Poisoning works behind the scenes: “The attacker has set up a reverse-proxy server, which secretly acts as an intermediary between you and the real company’s website. Everything looks normal to you, but in reality, your requests are passing through the attacker’s server.”
Once they have your information, the sky is the limit.
“Account takeover scams can be highly lucrative for fraudsters,” said Gosschalk. “They might seek to take control of high-value accounts and monetize valuable assets, such as gift card balances. Targeting lower-value accounts at scale is also a common tactic for criminals.”
Cybercriminals can use your information in several ways.
- Change personal account details
- Open a bank account in your name
- Open a new line of credit, such as a personal loan or auto loan
- Order a new credit card for spending
- Buy a new phone from your carrier
- Redeem rewards and account credits
- Make fraudulent payments from your financial accounts
- Make unauthorized purchases
- Steal unemployment benefits
- Sell personal details on the dark web
ATO can easily affect your credit and jeopardize your chances of getting new credit, whether it’s for a new home, car or credit card.
This attack is incredibly effective because it preys on trust and familiarity.”
Industries at risk
There’s no doubt that account takeover fraud is widespread. In its 2026 Identity Fraud Report, Entrust reports one billion identity verification attempts analyzed for 2025, with 30 industries and 195 countries affected.
“Every industry and account is at risk,” warned Lassiter. “Attackers do not discriminate on targets. They target everyone, then see what is valuable AFTER they have control.”
As the study showed, almost all industries are vulnerable to account takeover fraud, but some attract more attention than others.
- Financial services: Cybercriminals especially target the financial industry for direct access to funds. Sometimes, they don’t even steal funds, but rather, your account details, which can later be accessed, sold or used to launder dirty money.
- Health care: Health care is especially coveted on the dark web, enabling prescription fraud and fraudulent insurance claims. Medicare and Medicaid are also popular targets.
- E-commerce: Known as organized retail crime (ORC), this type of ATO fraud doesn’t target the consumers directly, instead targeting the retailer databases. This enables cybercriminals to access bulk data rather than hacking each account individually.
“While banks are the most frequent target, ATO also hits other industries that offer online accounts related to your finances that store personal data and allow changes to payment or payout details,” said Diana Rothfuss, global product marketing director at SAS. “This includes insurers, pension companies, government benefits and tax portals.”
Cybercriminals also often target the travel industry to steal rewards points and communications companies to seize control of phone contracts.
Signs of account takeover fraud
With so many ways to use your information, it’s crucial that you know the signs to protect yourself if your information or accounts are compromised.
Be sure to secure your accounts and change your passwords if you:
- Receive chargeback requests you do not recognize
- Get notifications of possible fraudulent transactions
- Are sent requests to change your password
- Receive notification of too many failed login attempts
- Have information added to your account, such as a new credit card or shipping details
- Have transactions on your statement that don’t match your spending
- Notice missing credit card rewards
“If you get an account-change notification that you didn’t prompt through your own activity, time is of the essence,” said Diana Rothfuss of SAS. “Contact the company right away using an official channel to ensure prompt intervention, and reset your credentials from a trusted device.”
» LEARN: How to check for identity theft
Preventing account takeover fraud
“This attack is incredibly effective because it preys on trust and familiarity,” commented Gosschalk.
More than half of those affected by ATO fraud used the same password across multiple accounts, significantly increasing their risk of fraud.
With these strategies, you can secure your accounts and protect yourself from account takeover fraud.
Complicate things
Intentionally make your passwords complex so they are more difficult to guess. This means including a longer combination of letters, numbers and special characters. Try not to use anything someone might easily know about you, such as your pet’s name or street name.
“Get a business-grade password manager and use it for everything. Let it create and store the passwords for you,” advised Lassiter. “This will avoid using weak or reused passwords, and some can even store the MFA codes as well.”
Also, be sure to enable additional security measures. This may include multi-factor authentication (MFA), facial recognition or fingerprint verification.
“MFA is the single best action you take, but don't use SMS if you can avoid it,” said Lassiter. “Use the app-based one-time passcodes.”
Keep a watchful eye
You can check for identity theft by monitoring your accounts regularly. Review your personal details to ensure they have not changed, and check your account activity for anything you do not recognize. This will help you take immediate action to minimize the impact of ATO fraud.
Be selective
Limit the personal information you share online. This includes social media, video and blog posts. Even little details like a pet’s name or old high school can give thieves clues as to what your security answers may be.
Bookmark it
One method cybercriminals use to steal your information is to trick you into entering fraudulent web addresses. These sites may appear authentic, but if you look more closely, you'll usually notice a letter or word that is off. However, you can create bookmarks on your web browser that you can use when accessing sensitive sites, rather than depending on a potentially false source.
However, Security.org’s study raises a concerning issue: 62% of those affected had already taken safety precautions such as two-factor authentication and security questions. It only reinforces the fact that you must remain vigilant and maintain safe, preventive practices to protect against future attacks.
Get help
Regular identity and credit monitoring can help you stay on top of your credit with automatic alerts that notify you in real time of suspicious activity. You may already have free credit monitoring from your bank or credit card company, but if not, some of the best credit monitoring sites include LifeLock, IDShield and Credit Sesame. You can also sign up with one of the credit bureaus: Experian, Equifax and TransUnion.
Responding to an account takeover incident
If you do find yourself the victim of account takeover fraud, take action immediately.
- Check your accounts. Perform a comprehensive sweep of all your accounts to ensure no other accounts have been affected, and update any necessary information.
- Contact your financial institution. Immediately notify your financial institution. This may include your bank or credit union, credit card company or lender.
- Limit your credit. You can place a credit fraud alert that notifies you of credit inquiries, so no illegitimate lines of credit are taken out in your name. You can also place a credit freeze, which will prevent the use of any credit until it is lifted.
- File a government report. File a report with the FBI’s Internet Crime Complaint Center (IC3) at ic3.gov.
- Reset your passwords. Change your passwords across all your accounts to new, complex combinations that are difficult to guess. Be careful not to repeat passwords.
- Update software. Ensure you’re using the latest versions of your software and programs to ensure the latest security features, and perform any necessary updates.
Remember, the sooner you act, the more you can minimize the damage.
“MFA is important,” Gosschalk acknowledged, “but it’s not foolproof. Understand that modern phishing attacks can bypass it and stay informed about new attack methods.”
“By staying informed and taking proactive steps to protect your accounts, you can keep your personal information safe and out of the hands of cybercriminals,” he encouraged. “In the digital age, awareness is your first line of defense—and it might just be the key to keeping your accounts secure.”
» COMPARE: Best identity theft protection services
FAQ
What is an example of account takeover?
An example of ATO fraud is receiving an email that appears authentic, only to have your information exposed when you click the link. These criminals can then take your information and steal your bank account funds, get a new cell phone, redeem your travel miles or even sell your information on the dark web.
What’s the difference between account takeover fraud and identity theft?
While account takeover fraud and identity theft are similar, they differ in the types of information they target. Account takeover fraud enables access to your accounts, while identity theft involves the theft of your personal data.
What are the signals of account takeover?
The signs of ATO fraud include password reset requests you didn't make, links with incorrect web addresses and missing funds, rewards or miles.
How does account takeover happen?
Account takeover happens when cybercriminals gain access to your personal accounts for malicious use. They can do this in several ways, including phishing, malware, brute-force attacks, social engineering or data breaches.
Article sources
ConsumerAffairs writers primarily rely on government data, industry experts and original research from other reputable publications to inform their work. Specific sources for this article include:
- Entrust, “2026 Identity Fraud Report.” Accessed Jan. 12, 2026.
- Experian, “What Is Account Takeover Fraud and How to Prevent It.” Accessed Jan. 12, 2026.
- Federal Trade Commission, “Facts About Fraud From the FTC – and What It Means for Your Business.” Accessed Jan. 12, 2026.
- Federal Bureau of Investigation Internet Crime Complaint Center (IC3), “Account Takeover Fraud.” Accessed Jan. 12, 2026.
- GIACT, “GIACT Now Part of LSEG - GIACT.” Accessed Jan. 12, 2026.
- Security.org, “Account Takeover Fraud: A Guide to Protecting Yourself.” Accessed Jan. 12, 2026.
- Thomson Reuters, “What Is Account Takeover? An Overview.” Accessed Jan. 12, 2026.